From eScan Wiki
Contents |
Settings
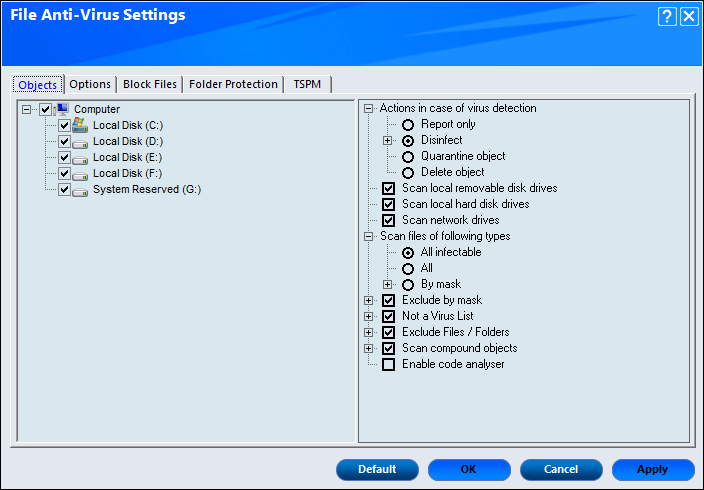
Configure settings for File Anti-virus using the settings option present under configuration. Following tabs are available for configurations:
- Objects
- Options
- Block Files
- Folder Protection
- TSPM
Objects
This tab will provide various option for fine tuning the settings available under File Anti-Virus. It provides options such as scanning a specific storage devices or excluding given file from scanning.
Actions in case of virus definition
Displays the different actions that can be performed in case of any infection. The actions are:
- Report only: Reports to you on a popup without taking any action on the file in case of virus detection.
- Disinfect: Automatically disinfect any infected file on detection. Under this action, following two options are available:
- Make backup file before disinfection: This check box allows to make backup file before disinfection.
- If disinfection is impossible: You can configure from the following options:
- Report Only: This option reports if it is not able to disinfect any particular virus.
- Quarantine object: This option quarantines the infected object (isolate the objects) if it is not able to disinfect a virus.
- Delete object: This option deletes the object if it is not able to disinfection a virus.
By default the Disinfect option is selected.
- Quarantine object: Quarantines the file whenever an infection is detected (isolate the file). You can restore the Quarantine/Backup file by using the below procedure:
- Click View Quarantine Objects option present on the main interface of File Anti-virus. You will be forwarded to the Quarantine window, click object name that you wish to restore. Now click Restore button to restore. File will be restored instantly.
- Delete object: Automatically delete the file whenever an infected file is detected.
The following are the options that allows to scan specific disk or drive:
- Scan local removable disk drives: This check box allows to monitor the real-time scanning of all the local removable drives attached to the computer. This option is enabled by default.
- Scan local hard disk drives: This check box allows to monitor the real-time scanning of all the local hard drives installed on the computer. This option is enabled by default.
- Scan network drives: This check box allows to monitor the real-time scanning of all the network drives including mapped folders and drives that are connected to the computer. This option is enabled by default.
Scan files of following types
This check box allows to choose the type of file to monitor while real-time scanning. It have 3 options to select files for scanning, whether All infectable, All, or By mask. The files listed in By mask option are the default file extensions that are defined by eScan. To add or delete files by mask, select and double-click Add/Delete option, and then add or delete files as required.
Exclude by mask
This check box allows to monitors all the excluded object in the Exclude by mask list during real‑time monitoring or scanning. You can add or delete a file or a particular file extension by double-clicking the Add/Delete option. This option is enabled by default.
Not a Virus List
File Anti‑Virus is able to detect the riskware. Riskware are legitimate program that are not strictly malicious, but pose some sort of risk for the user in another way. You can add the names of riskware, such as remote admin software to the riskware list in the Not a Virus List dialog box by double-clicking the Add / Delete option, if you are certain that they are not malicious. This option is enabled by default and the riskware list is empty by default.
Exclude Files/Folders
This option excludes the listed files, folders, and subfolders, while monitoring or scanning the folders. You can add or delete folders from the existing list of folders by double-clicking the Add / Delete option. This option is enabled by default.
Scan compound objects
This option allows to scan the archives and packed files during the scan. The Archive check box allows to scan archive files. The depth level of an archived file up to which you want to scan can be defined in Archive Depth Level field. By default, value is 16, but you can change it by double-clicking the arrow icon, and then type value in the size box. By default, Packed is selected. This option is enabled by default.
Enable code analyser
This option uses heuristic analyzer during the real-time scan of the computer for suspicious objects or unknown infections. It not only scans and detects infected objects by using the definitions or updates, but it also checks for suspicious files stored on the computer.
Options
This tab will allow to configure the basic settings such as the maximum size of log files and path of the destination folder for storing log files, quarantined objects, and report files.
It provides the following options for configuration:
Save report file
This option allows to save the generated reports. The generates report consist of logs information about the scanned files and the action taken when an infected file is detected. This option is enabled by default and it also allows to configure following settings:
- Show pack info in the report (Monvir.log): This option is enabled by default and it allows to add details about the scanned compressed files, such as .ZIP and .RAR files to the Monvir.log file.
- Show clean object info in the report (Monvir.log): This option allows to add details about uninfected files found during a scan operation to the Monvir.log file. This option helps to find out which files are not infected.
- Limit size to (KB) (avpM.rpt): This option helps to set the size limit of the avpM.rpt file. To specify the size of the log file, double-click the size box and define the size. The default value is 50 KB.
For quarantining of infected objects
This option helps to specify the destination for storing quarantined objects. By default, the quarantined objects are stored in the C:\Program Files\eScan\INFECTED [32-bit] OR C:\Program Files (x86)\ eScan\ INFECTED [64-bit] folder. You can change the location of the destination folder if required.
Enable Auto backup / Restore
This option allows to takes automatic backup of critical files of the Windows® operating system installed on the computer and to restore the clean files when it finds an infection in any of the system files, which cannot be disinfected. This option allows to configure the following settings:
- For backup of clean objects: eScan allows to backs up uninfected objects and store them in a given folder. By default, these objects are stored in a folder named Fbackup on the drive that has maximum free space. You can change the path of the destination folder if desired.
- Do not backup files above size (KB): This option is enabled by default and helps to prevent File Anti‑Virus from creating backup of files that is larger than the defined file size. The default value is set to 32768 KB.
- Minimum disk space (MB): This option is enabled by default and enables to set the minimum free hard disk space up to which you want eScan to take backup of files. By default, value is 1 MB, but you can change it by double-clicking the arrow icon, and then type value in the size box.
Use sound effects for the following events
This check box option allows to configure eScan to play a sound file and show the details regarding the infection within a message box when any malicious software is detected. However, you need to ensure that the computer speakers are switched on.
Display attention messages
This option allow to displays an alert, which consist the path, name of the infected object, and the action taken. This option is enabled by default.
Enable Malware URL Filter
This option is blocks the access to malicious websites/URL.
Proactive Behavior Monitor
This option allows to monitor the executable files that are running on your system. In case, if eScan finds any executable files suspicious that may cause any harm to your system, it alerts the user with a pop-up message. To access the suspicious file, you can White list them anytime.
It also allows to view the list of files that are blocked from executing on the system. You can add a File to White list or Block List using this option.
Enable Ransomware Protection
This check box enables the protection against ransomware and enabled by default.
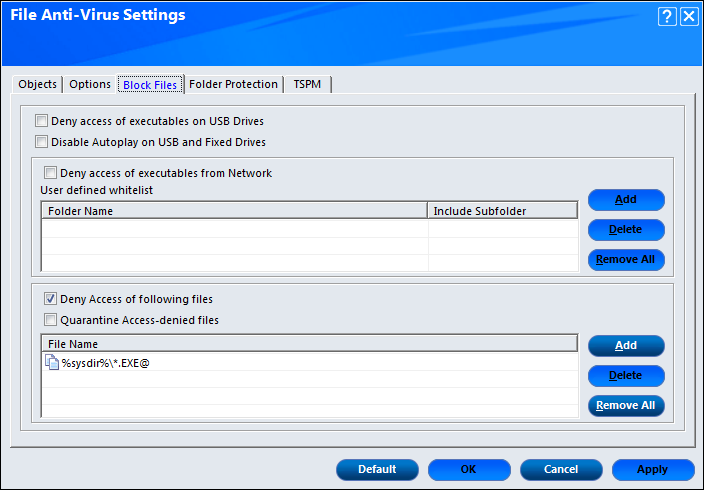
Block Files
This tab allows to configure the settings for preventing executable and files, such as autorun.inf, on network drives, USB drives, and fixed drives from accessing your computer.
It provides the following options for configuration:
Deny access of executables on USB Drive
This check box option helps to prevent executables stored on USB drives from being executed.
Disable Autoplay on USB and Fixed Drives
This check box option helps to disable Autoplay on USB and Fixed Drives. This option is enabled by default.
Deny access of executable from Network
This check box option helps to prevent executables from network from being executed on the computer. This option also allows to whitelist the folder/subfolder on the network as per the requirement. The whitelisted folder/subfolder can be access the executable from them.
Deny Access of following files
This check box option helps to prevent the files in the list from running on the computer. This option is enabled by default.
Quarantine Access-denied files
This check box option allows to quarantine files that have been denied access. To prevent specific files from running on the computer by adding them to the Block Files list. By default, this list contains the value %sysdir%\*.EXE@.
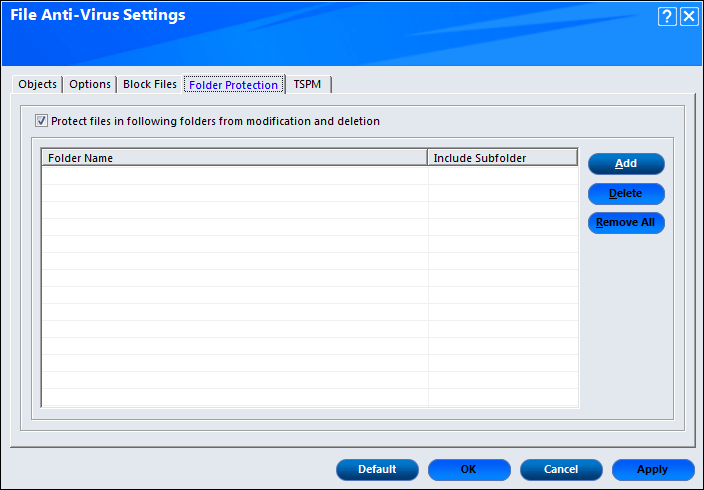
Folder Protection
This tab helps to protect specific folders from being modified or deleted by adding them to the Folder Protection list.
It provides the following options for configuration:
- Protect files in following folders from modification and deletion: This option is enabled by default. It protects the files in specific folders from being modified or deleted. Once you enable this check box, it will automatically enable the following buttons:
- Add: It allows you Add folders to be protected. Browse the folders and Add in the Folder List.
- Delete: You can delete the folder from folder list. Click on the Delete button. A confirmation window appears. Click Yes, the folder will be deleted.
- Remove All: You can remove/delete all the folders in the list at once.
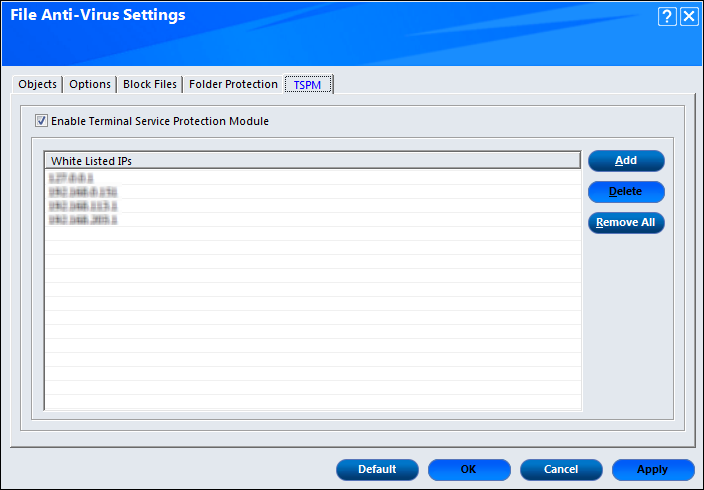
TSPM
TSPM – Terminal Services Protection Module by eScan detects brute force attempts and heuristically identifies suspicious IP Addresses/Hosts and blocks any attempts to access the system. In order to safeguard the systems from future attacks, the IP addresses and Hosts from these attacks are banned from initiating any further connections to the system.
Enable Terminal Service Protection Module
This option enables Terminal Service Protection Module. This will open a popup window from where you can add the IP address of the system you want to Whitelist. After adding the IP address, click on Add button. It will be added on the list.
|
NOTE |
At the bottom of the screen of all the tabs — Default, OK, Cancel, and Apply buttons are present that you can use after configuring the settings based on your requirement. |
- Default: Click this button to apply the default settings.
- OK: Click this button after you click the Apply button to apply the configured settings.
- Cancel: Click this button to cancel the configured settings or to close the window.
- Apply: Click this button to apply the configured settings.
Reports
This section displays the information along with the reports, which are as follows:
Total Files Scanned
It shows the total number of files scanned by the real-time File Anti-Virus monitor.
Dangerous Objects Detected
It shows the total number of viruses or malicious software detected by the File Anti-Virus monitor on a real-time basis.
Last File Scanned
It shows the name of last file scanned by File Anti-Virus monitor on real-time basis.
View Statistics
When you click this button, the statistics dialog box is displayed, which displays the latest activity report of the real-time monitor. The report contains information under two sections:
- Scanned: This section shows scanned details of objects of Virus bodies, Disinfected, Deleted, Quarantined etc.
- Found: This section shows Virus details such as Virus bodies, Disinfected, Deleted, Quarantined, etc.
View Quarantined Objects
Click on View Quarantined Objects, Quarantine popup gets displayed. It displays all the quarantined objects. There are two tabs present:
- Quarantine: This tab displays the files that have been quarantined. You can restore or delete the quarantined objects by right-clicking the object, and then clicking an appropriate option.
- Backup: This tab displays the files that were backed up by file anti-virus before it tried to disinfect them. You can restore or delete the objects that were backed up by right-clicking the object, and then clicking an appropriate option. Before clicking any of these buttons, you should ensure that you have selected an appropriate row in the table for which you need to perform the action.
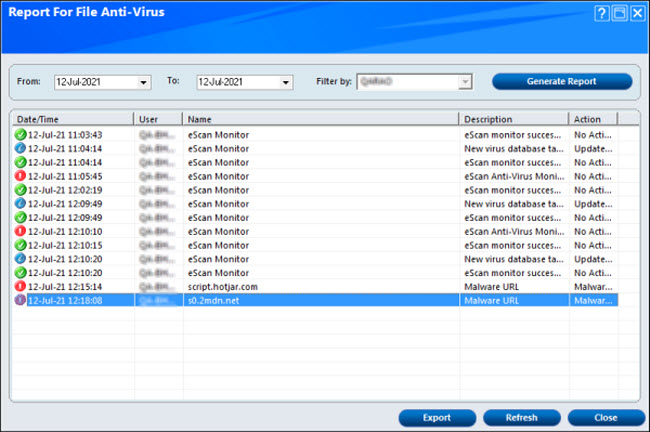
View Report
When you click this button, the report for file anti-virus window is displayed. This window displays the report for the file anti-virus module for a given range of dates in a tabular format when you click the generate report button.
You can export reports in the following formats:
- HTML
- CSV